
ElevenPaths, Telefónica global cybersecurity unit, and Gradiant keep on working together on the field of information technologies thanks to IRMAS – Information Rights Management Advanced Systems mixed research unit, where several research and development opportunities take shape in different innovation fronts. In this framework, TEGRA cybersecurity center –which both companies launched recently– performs a specialized role to promote information security activities, focusing on improvements for cybersecurity with a differentiating value and a scientific-technical excellence. As a result of this cooperation, we have a new technology that enables users’ biometric verification in the encrypted domain using SPED techniques.
In the new General Data Protection Regulation, which became enforceable the last May 25th, biometric data are framed within the definition of “special categories of personal data”. This categorization, in addition to imposing certain requirements to allow the processing, highlights that potential impact of risks associated to biometric data is high. Consequently, any organization must apply more restrictive protection measures to reduce the probability and impact of such risks, both for data security and people privacy.
Homomorphic encryption and protected biometric matching
Gradiant has got wide experience on developing biometric solutions for companies (face, voice and signature biometrics), and so it is at security and privacy fields, including advanced cryptographic techniques. By merging both fields, we have carried out this proof of concept where, through the application of a system based on homomorphic encryption we can verify user’s signature in the encrypted domain, keeping all data totally protected intransit, at rest and in use. Homomorphic encryption allows us to make operations on encrypted data in such a way that the company that is performing the computation has access neither to the data nor the result. Due to high computational costs all these cryptosystems require, this proof of conceptuses Somewhat Homomorphic Encryption (SHE), in which storage and computational costs are significantly reduced at the expense of a loss of the homomorphic capacity (number of operations that can be performed over encrypted data) and the type of allowed operations (linear operations that can expressed as a combination of sums and multiplications).
In order to carry out the proof of concept, we decided to implement a biometric signature verification system. More specifically, the matching operation, thanks to which we can get the similarity among the biometric reference profile and the captured biometric template in order to get the verification result, was implemented in a protected manner. First of all, it was necessary to select the biometric signature verification algorithm to be protected, opting for a matching operation based on linear operations, thus allowing its protection applying a SHE cryptosystem.
Proof of concept: SPED-signature
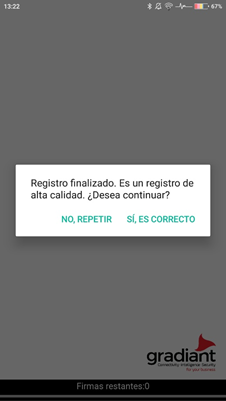
The demonstrator developed for this proof of concept is formed by the client app and the dynamic signature verification server. The process is divided into two steps: 1) registration, where we get the user’s handwritten signature from which we extract the biometric profile that will be used as a reference; 2) verification, where we get the user’s handwritten signature to extract the biometric template and match it with the reference profile captured on the registration step.
 |
During the registration step, the user’s handwritten signature is captured by the client app and her biometric profile is created. The biometric profile is encrypted using a key known only by the client application and it is sent to the server with the associated username.
For the verification step, the username is requested and the signature is captured. The biometric template obtained from the captured signature is encrypted, again with a key exclusively known by the client application, and sent to the server in order to be compared with the user’s biometric profile obtained during the registration step. The matching operation is carried out by the verification server with the data encrypted during the whole process. Finally, the result of the matching operation is sent, still encrypted and inaccessible for the server, to the client app which will be able to get the final result of the verification process.
 |
 |
Conclusions and next steps
The implemented system and the selected configuration have allowed us to keep the verification performance of the original unprotected system. Moreover, the increase in the computational cost, and therefore in the processing time (around 0.6 milliseconds), is imperceptible by the user. This makes it possible to transfer this type of protection to the market and opens the door to extend it to other biometrics and applications.
After this proof of concept, ElevenPaths and Gradiant will continue with the evaluation of the usability and applicability of this technology, looking for those use cases in which this technology adds a differential value, thanks to the innovative features incorporated in this proof of concept in terms of encryption. In addition, the GDPR imposes requirements not only on biometric data but also on many others to which this approach can contribute in an effective way, providing a mechanism and a technology that can solve highly complex functional requirements in an effective way.
Below we can see a video demonstration of the functionality implemented in the proof of concept:


