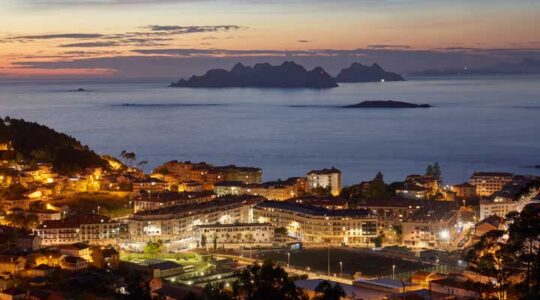
Salary and quality of life: where is more cost-effective to live?
One of the most important choices of a person in life is where to live. There are many factors, such as the people, the climate, the gastronomy, the services, or the job, to take into account when choosing a city or town. As we say in Galicia, this is a decision that “depends” in many […]