Guide to navigate the 5G Forum
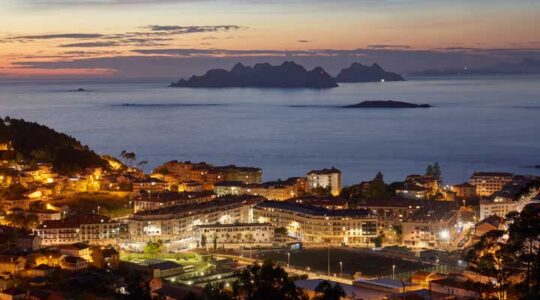
This year, we return to the 5G Forum to showcase our advances in technology focused on two main aspects: the security of 5G networks and UxVs. The event will take place at the Nissan Cartuja Auditorium in Seville, in a hybrid format with two in-person days (May 6th and 7th) and three virtual days […]