Spanish SMEs struggle to keep the world’s pace on adoption and adaptation to Cloud services, although it is an unstoppable trend, already at its second wave of adoption. According to INE’s survey on the use of ICT by spanish companies, in the case of cloud computing or cloud computing, only 19.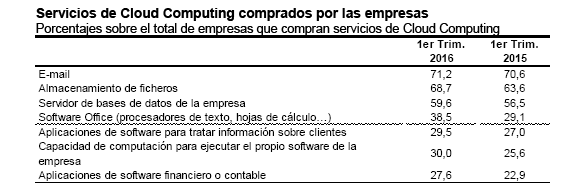
Among the Spanish companies acquiring cloud services, nearly seven in ten (69.
There are many reasons why companies decide to jump into the public cloud. They mainly focus is on saving maintenance costs of their own servers, the flexibility to grow easily, and nimbly manage applications and services that are necessary for business. In addition, cloud providers offer access to the system without downtimes, and perform automatic backups periodically.
But it is clear that any transfer of control over sensitive data implies concern: First, cloud computing has “transformed simultaneously businesses and governments”, and has even improved their business results. “But on the other hand, Cloud technology has created new security challenges,” note from the Cloud Security Alliance (CSA).
Indeed, not all companies feel comfortable when sending their business data to the public cloud (Amazon WS, Windows Azure, Google App Engine, Dropbox, Google Drive, SkyDrive, iCloud …), especially when seeking lower prices using services contracted by shared servers. Gradiant, the ICT Technology Centre of reference in Spain on security and cyber security, is already working on two main fronts, in order to allow companies to take full advantage of cloud computing, while minimizing risks:
On one hand, we offer very simple solutions to operate private clouds. These innovative developments such as ITBox, allow to have all the advantages of the public cloud, but leaving the data within the company and, therefore, re-using computing resources that are already available in the company. In addition, we are working on containers optimizations (eg Docker), which work isolated to bring public cloud environments (even sharing the same server) with better use of resources (less cost) than those achieved with traditional virtual machines. [Moreover, the use of Docker easily distributes a modular service in several containers (following architecture microservices), making an attack very difficult, when compared to a monolithic service deployed on a single server or a virtual machine.]
On the other hand, when we use the public cloud, we must bear in mind that while we are legally protected against any incident, the cloud provider will be able to access our data. As an example, Dropbox has explicit access to the files that we upload into our accounts. Aware of the existence and impact of this problem, Gradiant develops technology-based security mechanisms that prevent the cloud solutions provider to access companies private data. We are developing security mechanisms for working in the cloud environment with encrypted data, making it impossible for anyone (neither the supplier nor an external attacker) to see the information that is being processed in the cloud servers. Our approach is twofold: we either develop purely complex software-based cryptosystems or cryptographic hardware-based systems (HSMs) to protect extremely sensitive data (digital certificates, for instance).
Further info on Security, Cybersecurity and Cloud:
Gradiant, Security and Privacy
Gradiant: Security and Defense
Gradiant, new member of ECSO – European Cybersecurity
Gradiant takes its technologies for Security & Privacy to the Latin American market.
Commercial Contact:
Technology Contact


